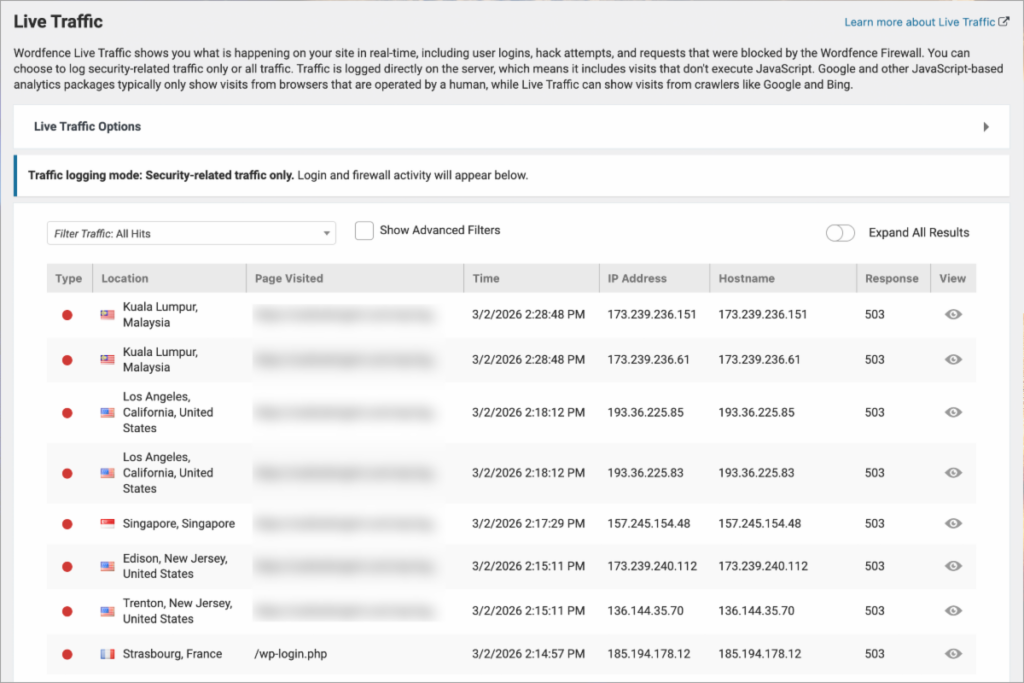
Automated login attempts against WordPress sites have increased significantly.
Even well-built sites are now tested constantly by bots looking for exposed accounts or weak access controls.
Login Pages Are a Primary Target
Most attacks focus on gaining access through /wp-admin. Automated tools attempt thousands of username and password combinations, often targeting administrator accounts first.
Without additional protection, a single compromised account can allow attackers to modify content, inject malicious code, or create new administrative users.
Two-Factor Authentication Adds a Critical Layer
Two-factor authentication (2FA) requires a second verification step beyond a password. Even if login credentials are exposed, unauthorized access is prevented without the secondary code.
This simple step stops the vast majority of automated login attempts.
Small Oversights Create Larger Risks
WordPress sites often accumulate inactive or unnecessary user accounts over time. Each unused account represents another potential entry point. Regularly reviewing and limiting access reduces exposure and keeps administrative control clear.
How to Reduce Your Exposure
A secure WordPress site typically includes a few consistent safeguards, such as:
- Enabling two-factor authentication for administrator accounts
- Removing inactive or unnecessary users
- Limiting administrative access to only those who need it
- Monitoring login activity and access attempts
If you are unsure whether your WordPress site has the right protections in place, we can help review your current setup and recommend next steps.